You Can’t Just Buy Zero Trust (But You Can Build It)
Time to read: 10 mins
Did you know that cybercrime, which is reaching new, costly heights every year, is predicted to become the “world’s third largest economy” behind China and the US?
Comparisons to the world economy, if we measured cybercrime as a country, draws a worrying image of a fast-approaching future where digital threats could cost the world $10.5 trillion. Accordingly, the market’s approach to cyber risk is hardening.
In this article our cybersecurity experts explore Zero Trust and a way to turn policies into practical solutions.
Recap – What is Zero Trust?
Zero Trust is a popular marketing catchphrase for IT security companies but it can be hard to pin down the meaning. That’s because Zero Trust is not simply a solution you can buy, it is more like a plan for rethinking basic security assumptions. The IT security industry is calling for Zero Trust in 2023, and the current interest reflects a broader cultural change where businesses and authorities are hardening their attitudes to all kinds of risk.
Zero Trust is more like a new approach to a security strategy which encapsulates a set of security principles, including:
- Verify every time
- Use least privilege for access
- Assume a breach has already occurred
Ultimately, the Zero Trust approach builds on the concept of privileged access management and adds more layers of security to build 365-degree protection. In a world where security threats have created deep paranoia, IT professionals need to remove implicit “trust” wherever possible. So the approach becomes “never trust, always verify”.

Zero Trust as a framework for an IT security architecture
Zero Trust is best defined as a framework to secure a complex network from internal and external threats, particularly where many security incidents come from the misuse of user credentials.
IBM explains Zero Trust as a philosophy where it is assumed that every user and every connection is a threat, and so the corporate network needs defence against these potential risks. It includes a number of security measures to provide continuous monitoring and validation to ensure that every user has the correct privileges and attributes:
- Logs and inspects all corporate network traffic
- Limits and controls access to the network
- Verifies and secures network resources
Zero Trust is, therefore, a framework where authentication, authorisation and validation are used to secure users’ access from inside and outside of the network, and this includes cloud-based connections and remote workers. It manages the permissions given to every device, the applications they can run and the data they can access, save, encrypt and transport.

A Zero Trust approach is recommended because now, with increased remote working and so many organisations relying on the cloud for their networks, the traditional network edge has eroded and there is a more diverse mix of users, technologies and applications which needs to be secured.
Even more challenging is how traditional security policies and tools are less effective across modern IT environments, and this creates a new headache for security professionals.
Best practice for IT security in the cloud
Zero Trust is fundamentally different to traditional privileged access management which only addresses the security of users within the network and does not guard against cases where a user’s credentials are misused. A Zero Trust approach should also secure the network from risks coming from the wider cloud-based environment.
Zero Trust is now required for large US organisations and in Europe. In the US, President Biden is mandating Zero Trust for major organisations and its use in the military is attracting a lot of attention. In the EU it helps to provide much of what is needed to satisfy the technical requirements of the GDPR.
It works by combining a number of IT security practices that work together to protect an organisation in today’s cloud-based technology environment.
Zero Trust – why now?
Cyber security threats have increased to new levels since 2023, with a worrying new surge in state-sponsored cyber activities targeting institutions. Phishing remains the greatest threat, causing 90% of data breaches. Microsoft mitigated an average of 1,435 distributed denial of service attacks each day in 2022, thought to be an increase of 67%. From 2023 there have been new 300,000 malware incidents each day, attempting to gain unauthorised access or disrupt IT systems.
IBM’s recent report on the cost of data breaches states that during 2022, 45% of data breaches were cloud-based, and that a breach of critical infrastructure cost $4.82 million, especially in financial services. The cost was estimated to be twice as much in healthcare.
At the start of this year TechTarget reported that:
- Gartner predicts that 45% of organisations will suffer a supply chain cyber attack by 2025
- Ethical hackers found over 65,000 vulnerabilities during 2022, up 21% on 2021
- Losses from identity fraud totalled $52 billion
- Crypto-jacking is growing at an amazing rate of 230%
All this makes for a frightening mix to keep us awake at night, but in spite of the clear benefits organisations are slow to adopt Zero Trust. IBM’s report stated that the majority of respondents (59%) were not using Zero Trust and in critical infrastructure 79% of organisations were not using it.
At CSI we know that there will be good reasons for this. Zero Trust needs a new security paradigm which requires time, resource, skills and the right products. Many organisations are looking at Zero Trust in the context of their own cloud-connected architectures where an extended network uses public and hybrid cloud and remote working. They often have fixed compliance needs. They will typically have a mixed estate and their legacy architecture doesn’t easily support the ideas in the Zero Trust model. It may not support modern authentication methods or secure protocol. It may seem that a whole new security architecture is required.
Added to this, IT security specialists are often fully occupied with ongoing monitoring and managing the response to alerts. There’s a concern that adding more products would make the whole set-up more complex to manage and maintain.
Why Identity (And Why Now)?
As enterprises review, renew and refine their strategic priorities, Zero Trust as a security approach continues to gain mindshare. Increasingly, and as more market research surfaces, analysts are building connections between breaches and compromised and abused privileged credentials.
A reported 80% of breaches targeting these user credentials, businesses should look to have a robust identity strategy at the top of their agenda.
With digital transformation projects, enterprises are faced with controlling data access and security for their own employees, contractors, suppliers, customers, and devices.
Identity is the ‘new’ perimeter in a cloud-native world. Allowing credentials without challenge or validation goes against best practices and industry wisdom, exposing an organisation to greater risk. Identity, as a shorthand for managing and validating user access and privileges, remains the only constant in today’s way of working.
Finding a feasible way to build Zero Trust
Company boards, along with CISOs, are likely to adopt a Zero Trust policy, but it is not easy to design and deploy.
We like this illustration because it takes the Zero Trust model of cyber security protection and breaks it down into a number of smaller, manageable parts based on NIST’s five stage security model, which is:
- Identify
- Protect
- Detect
- Respond
- Recover
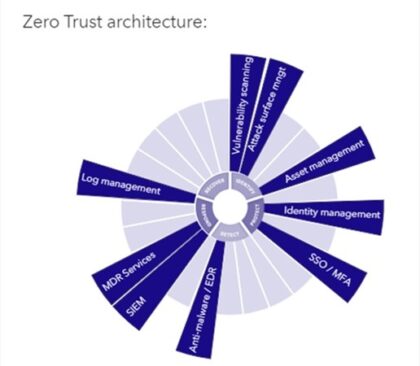
For each stage in the model there are one or more cybersecurity tools such as risk-based multi-factor authentication, identity protection, end-point security and encryption that can be utilised to build that section of the security architecture. It’s useful to bring clarity and define an approach that will deliver on the Zero Trust ambition.
CSI’s Head of Cyber Security, Leyton Jefferies, says:
“The most practical approach is to leverage the model to build Zero Trust around the technology and managed services that are already in place and do as much as you can with these. You can then identify the gaps where additional products or services are needed to close off new risks.”
CSI’s Zero Trust portfolio
At CSI, we are assembling a suite of tools from best-of-breed vendors to deliver against the Zero Trust model without adding unnecessary complexity. They are chosen to dovetail together and deploy in the new era of Zero Trust. Once in operation, they will provide a series of levers your CISO can pull to manage a Zero Trust policy day by day.
If you want to learn more about Zero Trust, register your place at our upcoming Security Event in London.
About the author
Read more articles
IBM Power
Levelling Up from Legacy IBM Power Systems (An EOS Guide)
Why Modernisation Matters Modernisation is often about market competitiveness and relevance. For modernised organisations, offboarding outdated hardware is a matter…
IBM Power
Why Private infrastructure is better for AI
Running AI Models vs. Building New AI Models: Inferencing and Training To make informed platform choices depends on a clear…
Storage and Backup
Improving Operational Resilience (With AI-driven Technology)
The Financial Impact of Cyber Attacks is Underestimated On average, analysts have discovered, a cyber-attack will force a UK SME…
Ready to talk?
Get in touch today to discuss your IT challenges and goals. No matter what’s happening in your IT environment right now, discover how our experts can help your business discover its competitive edge.
